Why Your 2FA Strategy Belongs in Your SOC 2 / Security Policies

Enabling 2FA isn’t enough for SOC 2 compliance. Without proper documentation and consistent enforcement, your organization risks compliance gaps, audit delays, and security vulnerabilities. SOC 2 auditors expect clear policies, centralized logs, and evidence that 2FA is applied intentionally across critical systems.
Here’s why 2FA matters for SOC 2:
- 47.2% of cloud breaches in 2024 were caused by weak or stolen credentials.
- SOC 2 criteria (CC6.1, CC6.2, CC6.3) require strong access controls and audit-ready evidence.
- Failing to revoke 2FA tokens promptly during offboarding is a common compliance issue.
To avoid these pitfalls, your 2FA strategy should include:
- A formal policy specifying where 2FA is required, approved methods (e.g., TOTP apps, hardware tokens), and offboarding processes.
- Centralized, automated logging for authentication events, including user IDs, timestamps, and methods used.
- Role-based access control (RBAC) and regular access reviews to ensure compliance.
Properly integrating 2FA into your SOC 2 framework strengthens security, simplifies audits, and reduces risks tied to compromised credentials.
The Problem: Informal 2FA Practices Create Compliance Risks
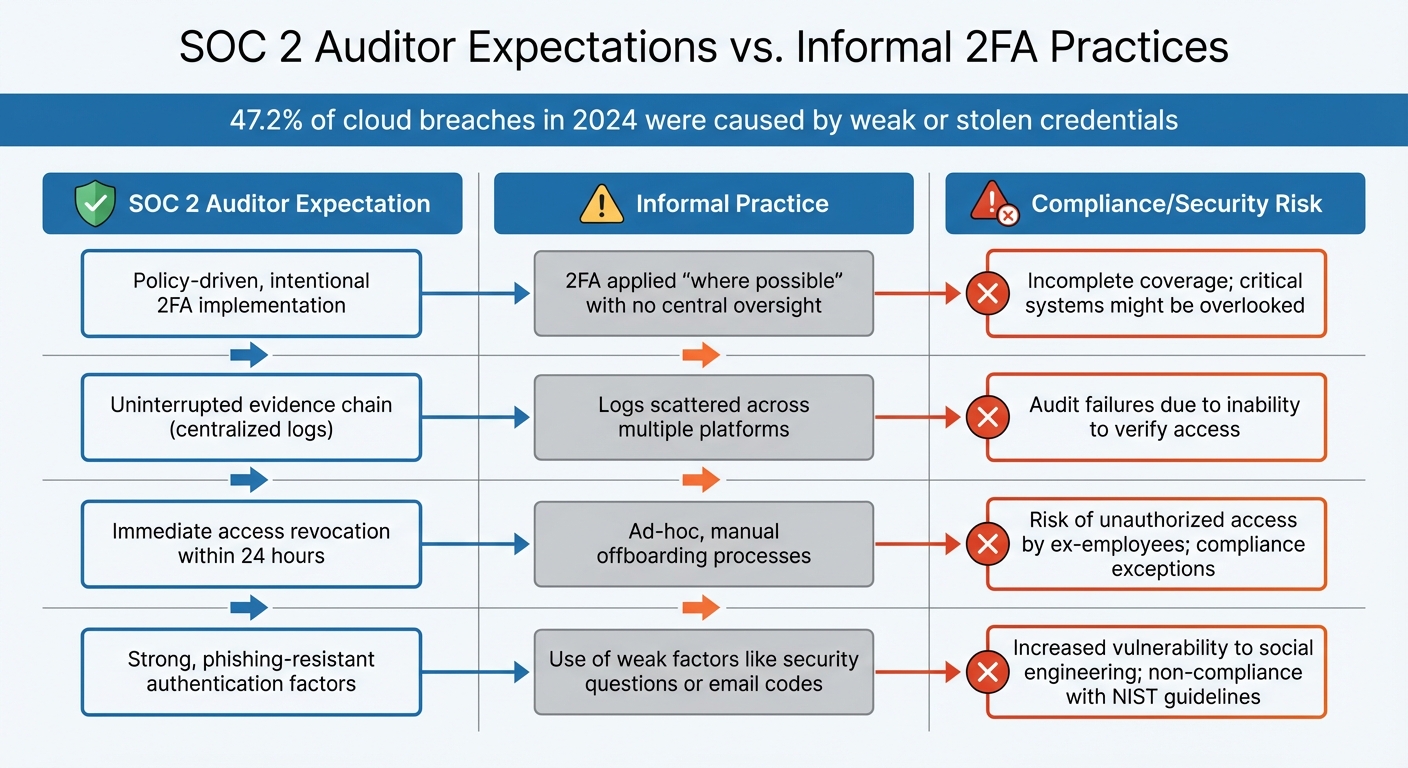
SOC 2 Auditor Expectations vs Informal 2FA Practices: Compliance Risks
Many companies assume they're compliant simply because they've enabled two-factor authentication (2FA) across their systems. But just turning on 2FA isn't enough. Without formal policies and proper documentation, businesses risk audit headaches and security vulnerabilities that auditors are quick to flag.
What SOC 2 Auditors Expect vs. What They Find
Auditors don’t just want to see that 2FA is enabled - they expect evidence of deliberate implementation and enforcement. This means having centralized logs, written policies that specify which systems require multi-factor authentication (MFA), and clear procedures for granting and revoking access.
What they often uncover instead is a patchwork approach. Companies might have 2FA in place "where possible", but without a central mandate or consistent offboarding processes. For example, when employees leave, access isn't always revoked promptly. Fragmented logs and inconsistent account management make it difficult to track who accessed what, when, and how - violating Common Criteria CC6.1 [6].
"For modern SOC 2 Type II reports, relying solely on Single-Factor Authentication (passwords) for administrative access, source code repositories, or production data is almost universally considered a 'significant deficiency' or an exception."
This insight from Logto [6] highlights the exact issues auditors frequently flag. These gaps show why undocumented 2FA practices pose both compliance and security risks.
Such inconsistencies not only complicate audits but also leave organizations exposed to serious vulnerabilities.
Risks of Undocumented 2FA Policies
The risks of informal 2FA practices go far beyond failing an audit. Without written policies, you can’t demonstrate compliance with the Joiner/Mover/Leaver (JML) process. Auditors often cross-check terminated employee lists against system logs. If 2FA tokens weren’t revoked within 24 hours of an employee leaving, it’s flagged as a compliance issue [6].
Another common problem is "manual backfilling" of evidence during audits. This creates bottlenecks, drives up remediation costs, and increases stress for teams [1]. On top of that, informal practices often rely on weak authenticators. According to NIST, these are unacceptable because they’re highly susceptible to social engineering attacks [5]. When auditors identify these flaws, they classify them as serious deficiencies, which can delay SOC 2 certification and erode customer confidence.
| SOC 2 Auditor Expectation | Informal Practice | Compliance/Security Risk |
|---|---|---|
| Policy-driven, intentional 2FA implementation | 2FA applied "where possible" with no central oversight | Incomplete coverage; critical systems might be overlooked [4] |
| Uninterrupted evidence chain (centralized logs) | Logs scattered across multiple platforms | Audit failures due to inability to verify access [1] |
| Immediate access revocation within 24 hours | Ad-hoc, manual offboarding processes | Risk of unauthorized access by ex-employees; compliance exceptions [6] |
| Strong, phishing-resistant authentication factors | Use of weak factors like security questions or email codes | Increased vulnerability to social engineering; non-compliance with NIST guidelines [5] |
How 2FA Supports SOC 2 Trust Services Criteria
2FA plays a key role in meeting SOC 2 criteria. By understanding how it aligns with these requirements, you can create policies that auditors can easily verify and approve.
How 2FA Meets the Security Criterion
2FA addresses CC6.1, CC6.2, and CC6.3, which are essential for SOC 2 compliance:
- CC6.1 (Logical Access Controls): This criterion requires technical barriers to protect information assets. 2FA acts as one of these barriers, ensuring that only verified identities gain access [4].
- CC6.2 (Authentication Mechanisms): This criterion focuses on user registration and authorization before granting access. 2FA meets this requirement by verifying identity through multiple independent factors - such as something you know (password), something you have (hardware token or phone), or something you are (biometric). It's important to use independent factors, like pairing a password with a hardware token, rather than relying on two "something you know" factors [1].
- CC6.3 (Access Modification): For high-risk areas, MFA (a broader term that includes 2FA) is often required. Its absence is frequently flagged as a deficiency in SOC 2 Type II reports, especially for administrative access, source code repositories, and production data. Microsoft data even shows that MFA can prevent up to 99.9% of account compromises, highlighting its effectiveness [7].
| SOC 2 Criterion | Role of 2FA | Audit Evidence |
|---|---|---|
| CC6.1 (Logical Access) | Serves as a technical barrier for data protection | System configuration screenshots; Architecture diagrams showing MFA placement |
| CC6.2 (Authentication) | Verifies identity using multiple factors (Know, Have, Are) | Time-stamped authentication logs; User registration/onboarding records |
| CC6.3 (Access Control) | Adds "step-up" authentication for privileged accounts | Access control matrix; Logs showing MFA for administrative logins |
To meet these criteria, it's crucial to support 2FA with comprehensive logs and policies.
Why Documentation Matters for SOC 2 Audits
Technical controls like 2FA are only part of the equation - documented evidence is equally important. Auditors need proof that your controls were consistently active throughout the observation period. This involves maintaining timestamped logs, formal security policies, and detailed access matrices [4].
Auditors will compare your Access Control Policy with actual system configurations and logs. For example, if your policy mandates MFA for all production database access but logs show administrators bypassing it, that’s a compliance exception [1].
"Every access event should be documented with minimal manual intervention, resulting in an audit window that clearly reflects control activities."
– ISMS.online [1]
This insight from ISMS.online underscores the importance of centralized logging. Logs should include the User ID, timestamp (in UTC), authentication method, and status (success or failure). Such a trail proves that controls are effective [4].
The stakes are high. The global average cost of a data breach reached $4.44 million in 2025, with U.S. costs exceeding $10.22 million [4]. Detailed logs and policies not only satisfy audit requirements but also demonstrate diligence in safeguarding your systems.
Building a 2FA Policy for SOC 2 Compliance
After identifying audit gaps, a formalized 2FA policy serves as the bridge between technical controls and meeting compliance requirements. A well-structured policy turns technical measures into clear, auditable documentation. Consistent and thorough documentation is at the heart of SOC 2 compliance.
What to Include in Your 2FA Policy
Start by defining the scope of the policy. List all team members, contractors, and third-party vendors who have access to production systems or sensitive customer data. This inventory will act as your baseline for enforcement.
Next, specify the approved authentication factors based on NIST guidelines. Acceptable methods include TOTP apps (like Google Authenticator), hardware tokens (such as FIDO2 keys), and biometrics. Avoid relying on knowledge-based factors, such as security questions, as they fall into the same category as passwords ("something you know") and don’t qualify as a second factor.
Require multi-factor authentication (MFA) for all critical accounts, including administrative interfaces, production databases, and systems enabling remote access. Establish a formal process for managing exceptions, requiring approval from the CISO and proper logging in an access control register. Additionally, outline account recovery procedures for users who lose access - this could involve single-use recovery codes or identity verification through support teams. Ensure that MFA enrollment is mandatory during onboarding and that tokens are immediately revoked when employees leave the organization.
| Policy Element | Description | SOC 2 Alignment |
|---|---|---|
| Scope | Covers all users, contractors, and critical systems | CC6.1 (Logical Access) |
| Approved Factors | TOTP, FIDO2, or Biometrics (no security questions) | CC6.2 (Authentication) |
| Logging | Captures user ID, timestamp, method, and status | CC6.2 (Evidence Chain) |
| Recovery | Includes procedures for lost devices (e.g., backup codes) | CC6.3 (Access Modification) |
| Exceptions | Requires CISO approval for bypasses like service accounts | Risk Management |
Defining 2FA Requirements for Critical Systems and Roles
Not every system demands the same level of protection. Focus your 2FA efforts on high-risk access points, such as production databases, administrative interfaces, Git repositories, and systems containing regulated data. While SOC 2 doesn’t explicitly require MFA, strong access controls under CC6.1, CC6.2, and CC6.3 mean that auditors expect MFA for privileged accounts and remote access as a best practice.
Start by inventorying all systems and user roles to pinpoint those managing customer data or critical operations. Pay special attention to administrative and DevOps roles, especially since weak credentials were behind 47.2% of initial access vectors in cloud breaches during mid-2024 [4]. For cloud root accounts (AWS, GCP, Azure), enforce hardware security keys and maintain documented "break-glass" recovery procedures [2]. Clearly define acceptable factors - such as TOTP apps and FIDO2 keys - for high-risk roles, and restrict SMS-based authentication to low-risk accounts or backup scenarios. This risk-based approach aligns with the principle of least privilege, ensuring access permissions adjust as roles evolve.
Once these requirements are set, integrate them with your broader access control and logging strategy.
Connecting 2FA with Access Controls and Logging
A solid 2FA policy works hand-in-hand with access controls and logging to create audit-ready evidence. Your identity provider should log key details, including user ID, timestamp (in UTC), system accessed, the MFA method used, and whether the attempt was successful or not. This ensures an unbroken chain of evidence that maps directly to SOC 2 criteria CC6.1 and CC6.2, proving consistent enforcement of access controls.
To strengthen this system, integrate 2FA with role-based access control (RBAC) so that users only have access to the systems required for their roles. Use Single Sign-On (SSO) to centralize authentication, and schedule quarterly access reviews to confirm that permissions remain aligned with job responsibilities. For environments with Bring Your Own Device (BYOD) policies, implement conditional access strategies that trigger 2FA based on user behavior, device security, or network location. Automate evidence collection with compliance tools that capture system configurations and access logs in real time, ensuring you're always prepared for audits.
sbb-itb-070b8f8
Managing 2FA Across Teams with Shared Numbers and Logging
The Risks of Shared Credentials and Phone Numbers
Using shared phone numbers for two-factor authentication (2FA) can quickly turn into a compliance headache. When multiple team members rely on the same number to receive verification codes, it becomes impossible to trace individual login attempts back to a specific person. This creates a gap in accountability that auditors often flag, as it breaks the evidence chain required under CC6.1 and CC6.2.
Another issue arises when companies use VoIP services for shared 2FA numbers. While these services are fine for business calls, many platforms block them for verification purposes due to concerns about fraud. As highlighted in NIST Special Publication 800-63B, "Methods that do not prove possession of a specific device, such as voice-over-IP (VOIP) or email, SHALL NOT be used for out-of-band authentication" [5].
These challenges make it clear: managing 2FA securely requires a controlled, auditable approach.
How to Manage Shared 2FA Securely
To address these risks, consider using company-controlled real-SIM numbers in combination with centralized code delivery. By routing SMS codes to a secure, dedicated channel - like a private Slack or Discord channel - you create a transparent, time-stamped record of every code received. This setup also documents which team member accessed the code. For example, JoltSMS offers dedicated real-SIM U.S. numbers that work reliably with over 1,000 platforms, including banking apps, AWS, and Stripe, where VoIP numbers often fail.
Implementing Role-Based Access Control (RBAC) adds another layer of security. With RBAC, only authorized personnel can access the centralized 2FA inbox. If someone leaves the team, you can simply revoke their access to the channel while retaining full control over the number and its message history. This approach ensures that every access event is logged and verifiable, meeting auditor expectations for compliance.
Once secure management is in place, the next step is to establish strong logging practices to solidify compliance.
Setting Up Logging for Compliance
Secure 2FA management is only part of the equation - detailed logging is essential for turning authentication events into audit-ready evidence. Effective logging should capture important metadata while safeguarding sensitive information. The OWASP guidance is clear: "OTP implementations SHOULD NOT log OTP values" [7].
A robust logging setup should include key details like user ID, timestamps, systems accessed, and the method of authentication used. Here’s a quick example of what a well-structured log might look like:
| Logging Field | Description | Example |
|---|---|---|
| User ID | Unique identifier of the individual or account | [email protected] |
| Timestamp | Time of the authentication attempt (UTC) | 02/05/2026 09:15:22 |
| System/App | The platform being accessed | AWS Production Console |
| Method Used | MFA factor applied | Password + Real-SIM SMS |
| Status | Authentication result | Success |
| Metadata | Additional details like IP or location | 192.168.1.1 (New York, US) |
Automating this process ensures every access event is logged consistently. Store these logs in tamper-proof, immutable storage, and integrate them with your SIEM for continuous monitoring. This creates an audit trail that reflects your control activities in real time.
During Type II audits, auditors will typically sample logs over a period to confirm that MFA was enforced and no unauthorized access occurred. By automating evidence collection, you transform authentication into an ongoing, audit-ready process, making compliance far easier to maintain.
Conclusion: Strengthening Security and Compliance with 2FA
Benefits of Embedding 2FA in SOC 2 Policies
Formalizing a 2FA strategy transforms access control into a consistent and audit-ready process, streamlining compliance efforts and reducing administrative burdens. This proactive approach minimizes last-minute evidence collection, making it easier to stay prepared for audits.
The security advantages are hard to ignore. Statistics show that 47.2% of initial access vectors in cloud breaches stemmed from weak or stolen credentials, while 88% of web application breaches involved compromised login details [4][5]. A well-documented 2FA policy not only addresses these vulnerabilities but also reduces remediation costs and long-term technical challenges. Considering that the average cost of a data breach in the U.S. now surpasses $10.22 million, the financial incentive for implementing MFA is undeniable [4].
MFA not only lowers the risk of unauthorized access but also provides the time-stamped logs auditors need to verify consistent enforcement of controls.
Beyond meeting compliance requirements, integrating 2FA into organizational policies improves user management. When paired with Single Sign-On (SSO) and automated provisioning, processes like onboarding and offboarding become smoother, and the integrity of your evidence chain is preserved throughout the observation period [4].
Next Steps for Implementing 2FA in Your Organization
To fully leverage the benefits of 2FA, consider these steps to integrate it into your SOC 2 framework. For guidance on evidence collection, refer back to centralized logging practices discussed earlier.
- Start with an inventory of systems and roles. Identify all critical user roles and systems, then update your access control policy to outline required MFA accounts, acceptable authentication methods (like TOTP, FIDO2, or biometrics), and clear offboarding protocols [4]. Avoid insecure channels, such as email or VoIP, for out-of-band authentication, as they fail to meet NIST guidelines [5][3].
- Use company-controlled SIM numbers for shared accounts. For teams managing critical services, rely on real-SIM numbers controlled by your organization to generate reliable, audit-ready 2FA codes. Route SMS codes to a shared Slack or Discord channel to maintain a transparent, timestamped audit trail while retaining full control over access. For more tips, check out securing IT operations with dedicated numbers and mitigating SMS phishing risks.
- Maintain continuous audit readiness with structured logging. Organizations that adopt structured, human-led logging practices can achieve SOC 2 readiness in 4 to 5 months, significantly faster than the 9 to 12 months typical of self-managed programs [4].
FAQs
Why isn’t enabling 2FA enough to meet SOC 2 compliance requirements?
Enabling two-factor authentication (2FA) is a smart step in strengthening security, but it alone doesn’t check all the boxes for SOC 2 compliance. SOC 2 demands a more comprehensive approach to access controls, which includes continuous monitoring, detailed logging, and audit trails to track and verify every access event.
Think of 2FA as just one piece of a much larger security framework. For SOC 2 compliance, your policies need to go beyond just implementing 2FA - they must also explain how it’s monitored and integrated into your broader security measures. This approach not only blocks unauthorized access but also ensures every action is documented and can be traced back if needed.
How can organizations effectively document and enforce their 2FA policies?
To properly document and enforce 2FA policies, organizations should incorporate clear workflows, thorough guidelines, and consistent logging into their security practices. Start by embedding 2FA procedures into your security policies, making sure they're standardized and easy for all team members to access. This approach minimizes confusion and supports compliance with frameworks like SOC 2.
Enforcement becomes more robust with event logging that records every 2FA interaction, creating an audit trail that's resistant to tampering. This not only helps ensure compliance but also highlights potential security weaknesses. By blending detailed documentation, automated logging, and routine reviews, organizations can establish a dependable system that bolsters security and supports regulatory requirements.
What are the dangers of using weak or informal 2FA methods in a SOC 2 framework?
Relying on weak or casual two-factor authentication (2FA) methods within a SOC 2 framework can put both your security and compliance efforts at risk. SOC 2 emphasizes the need for strong access controls, including multi-factor authentication (MFA), to safeguard sensitive data. Informal approaches - like sharing credentials or using unmonitored authentication methods - open the door to threats such as social engineering attacks or credential theft.
On top of that, these informal practices often lack the detailed logging and audit trails needed to demonstrate compliance during SOC 2 audits. Without proper records of authentication activities, proving the effectiveness of your access controls becomes a challenge. The consequences? Potential audit failures, data breaches, and harm to your organization's reputation. To align with SOC 2 requirements and strengthen security, it's crucial to establish formal, well-documented 2FA policies that include thorough logging and monitoring.